In an era where digital fraud and sophisticated identity spoofing are at an all-time high, organizations—especially those serving the federal sector—must look beyond basic security. The National Institute of Standards and Technology (NIST) has long provided the gold standard for digital identity, and the transition to the NIST 800-63-4 IAL3 compliance framework marks a significant leap in how we verify human identity in a digital world.
For organizations handling sensitive data or critical infrastructure, achieving Identity Assurance Level 3 (IAL3) is no longer just a recommendation; it is a necessity for maintaining trust and meeting FedRAMP High identity proofing requirements.
What is NIST IAL3 Verification?
NIST IAL3 verification is the highest level of identity assurance defined by the NIST SP 800-63 suite. While IAL1 requires no proofing and IAL2 allows for remote verification with “high confidence,” IAL3 is designed for “very high confidence.”
The core of IAL3 is the requirement for either physical presence or supervised remote proofing. This means an applicant must interact with a trained representative who can verify the authenticity of physical documents and ensure the person presenting them is the true owner. Under the latest NIST 800-63-4 IAL3 compliance standards, this process has been modernized to include more flexible “supervised remote” options, provided they meet rigorous security and liveness criteria.
The Pillars of NIST 800-63-4 IAL3 Compliance
The 800-63-4 revision introduces a risk-based Digital Identity Risk Management (DIRM) framework. To meet the IAL3 standard, your verification process must adhere to several strict pillars:
- Superior Evidence: Applicants must provide “Strong” or “Superior” identity evidence, such as a valid passport or enhanced driver’s license, which is then verified against the issuing authority or authoritative sub-sources.
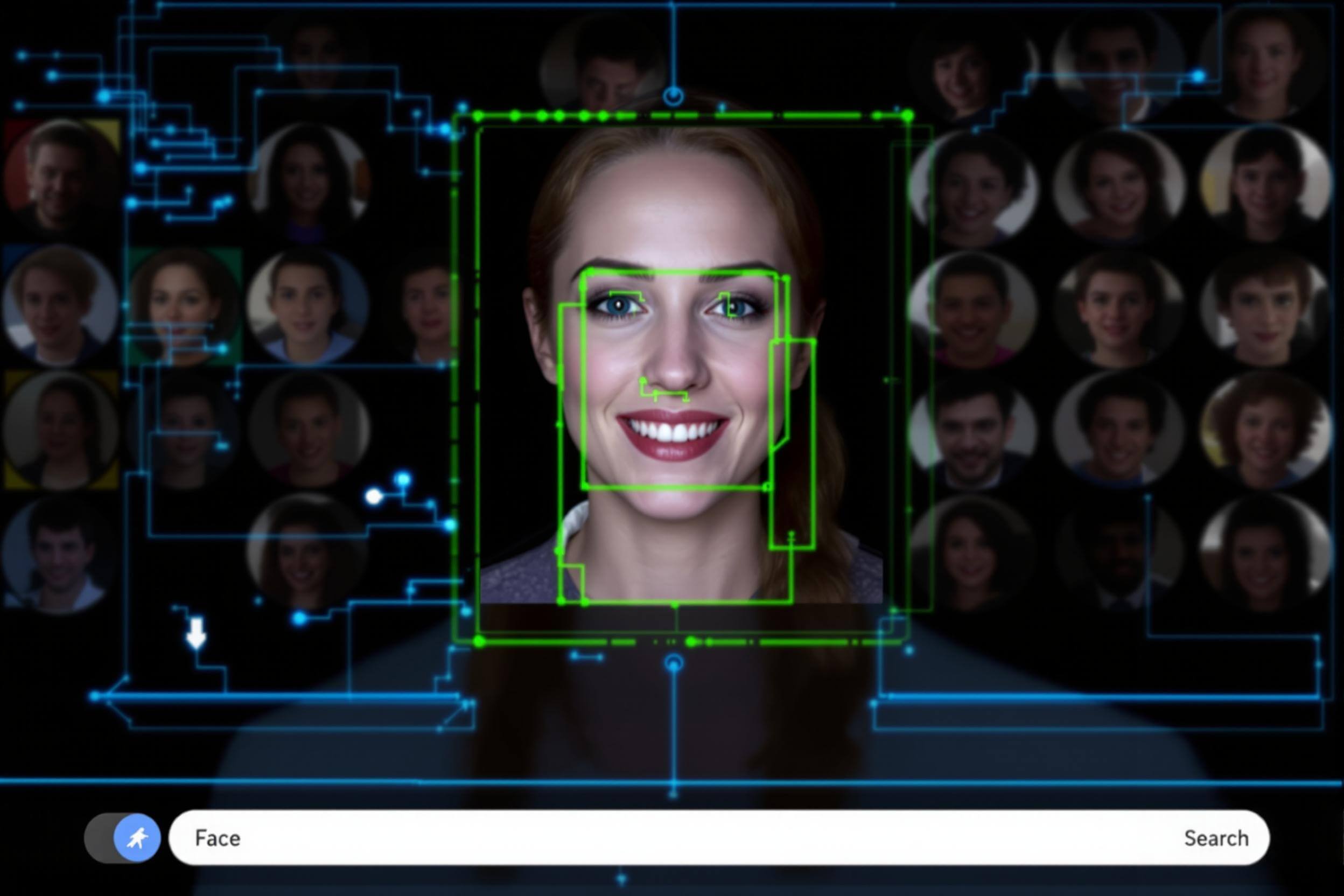
- Biometric Binding: Unlike lower levels, IAL3 mandates biometric collection (such as facial recognition or fingerprints). This biometric must be matched against the evidence provided to ensure the “holder” of the document is the “owner.”
- Human Oversight: A trained professional must oversee the session. This oversight mitigates risks like “injection attacks,” where hackers try to feed pre-recorded videos or deepfakes into a verification system.
- Phishing Resistance: While IAL refers to identity proofing, it is often paired with Authenticator Assurance Level 3 (AAL3), which requires hardware-based, phishing-resistant authenticators.
Why You Need IAL3 Identity Verification Software
Achieving this level of security manually is an operational nightmare. IAL3 identity verification software automates the heavy lifting of document forensic analysis and biometric matching while providing the secure interface for human supervisors to conduct remote sessions.
Modern software solutions, like Trust Swiftly, enable organizations to:
- Perform real-time document validation using AI-driven forensic checks.
- Conduct supervised remote sessions via secure video links that prevent data tampering.
- Integrate biometric liveness detection to thwart deepfakes and presentation attacks.
- Maintain a complete, auditable “Chain of Custody” for every identity verified.
FedRAMP High Identity Proofing and the Federal Mandate
For Cloud Service Providers (CSPs) and agencies, FedRAMP High identity proofing is the benchmark for securing the government’s most sensitive unclassified data. If your system is rated at the FedRAMP High impact level, NIST guidelines state that you must implement IAL3 for any transactions that carry high risk or involve access to highly sensitive information.
Meeting IAL3 compliance ensures that your cloud environment is protected against the most advanced identity-theft techniques. It bridges the gap between “knowing a user has a password” and “knowing exactly who that user is in the physical world.”
Implementing IAL3 Without the Friction
Historically, the “physical presence” requirement of IAL3 was a barrier to user experience. However, with the evolution of IAL3 identity verification software, businesses can now utilize kiosks or secure remote kits.
For example, a company can deploy a managed kiosk at a local office. The employee presents their ID to the kiosk’s high-resolution camera, and a remote agent—located hundreds of miles away—oversees the session in real-time. This “supervised remote” model meets the strict NIST 800-63-4 IAL3 compliance criteria while significantly reducing the cost and time associated with traditional in-person onboarding.
Future-Proofing Your Identity Strategy
As we move toward a Zero Trust architecture, identity is the new perimeter. Relying on outdated “knowledge-based” questions or simple SMS codes is a liability. By adopting nist ial3 verification, you are implementing a “Verify Once, Trust Always” philosophy that protects your organization from the ground up.
Whether you are seeking to meet FedRAMP High identity proofing standards or simply want the highest level of protection for your enterprise, Trust Swiftly provides the tools to make IAL3 compliance achievable, scalable, and secure. Don’t wait for a breach to upgrade your standards—embrace the future of high-assurance identity today.






